New technology protects authenticity of engineered cell lines
Innovations in artificial biology and genome enhancing have led to a expanding market to develop custom made mobile traces for health-related exploration. These engineered cell lines, on the other hand, can be susceptible to misidentification, cross-contamination and illegal replication.
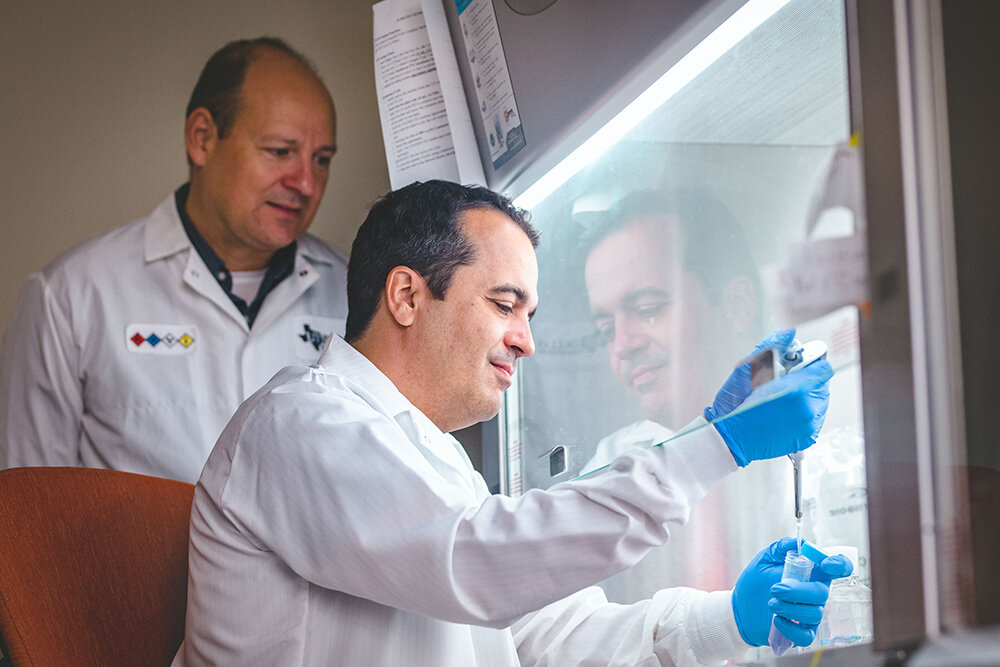
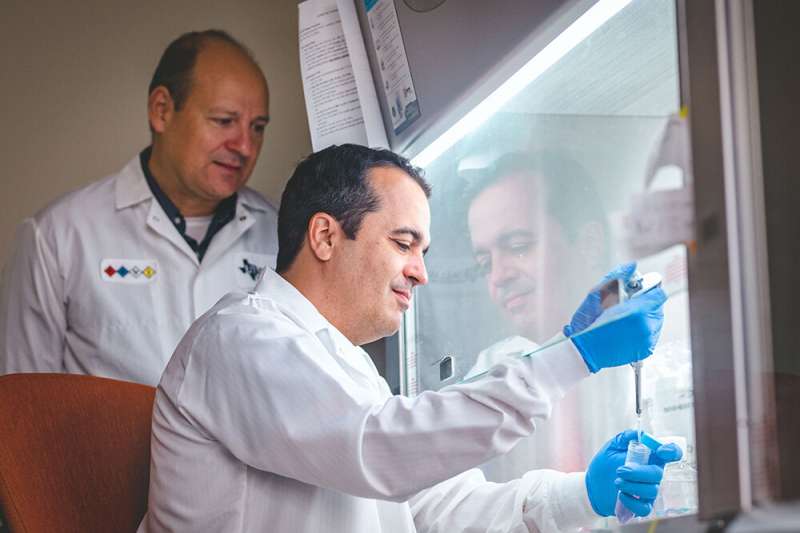
A staff of University of Texas at Dallas researchers has formulated a 1st-of-its-type technique to produce a unique identifier for each individual copy of a mobile line to allow for end users to confirm its authenticity and shield the manufacturer’s intellectual home (IP). The engineers demonstrated the method in a research printed on the net May perhaps 4 and in the May 6 print edition of Science Improvements.
The patent-pending technological innovation is the result of an interdisciplinary collaboration concerning UT Dallas faculty associates. The study’s co-corresponding authors are Dr. Leonidas Bleris, a professor of bioengineering who specializes in genetic engineering, and Dr. Yiorgos Makris, a professor of electrical and laptop engineering who is an specialist on electronics hardware stability.
Custom mobile traces are applied in the advancement of vaccines and specific therapies for a variety of conditions. The world mobile-society sector is projected to access $41.3 billion by 2026, an boost from $22.8 billion in 2021, according to a forecast by marketplace study company MarketsandMarkets.
The UT Dallas engineers’ investigate to acquire one of a kind identifiers for genetically engineered cells was influenced by what are termed physically unclonable features (PUFs) in the electronics marketplace. A PUF is a actual physical attribute that can serve as a exclusive “fingerprint” for a semiconductor device these kinds of as a microprocessor. In semiconductors, PUFs are centered on organic variants that arise during the production system and ought to meet three demands: They need to have a exclusive fingerprint, deliver the identical fingerprint every time they are calculated and be pretty much impossible to replicate.
To use that idea to engineered cells, the researchers formulated a two-phase method that normally takes gain of a cell’s ability to repair service ruined DNA, which is made up of sequences of compact molecules termed nucleotides.
To start with, they embedded a 5-nucleotide bar-code library into a component of the cell’s genome identified as a safe and sound harbor, in which the modification will not damage the mobile. The bar codes alone, on the other hand, do not satisfy the a few attributes of PUFs. In the 2nd move, researchers utilized the gene-modifying resource CRISPR to minimize the DNA in the proximity of the bar code. That action forces the cell to repair its DNA utilizing random nucleotides, a method named nonhomologous mistake repair service. Through this restore course of action, the mobile obviously inserts new nucleotides into the DNA and/or deletes others—collectively, these are referred to as indels (insertions/deletions). These random fixes, in mixture with the bar codes, develop a special pattern of nucleotides that can assist distinguish the mobile line from any other.
“The combination of bar-coding with the inherently stochastic cellular mistake fix process outcomes in a distinctive and irreproducible fingerprint,” stated Bleris, who is also the Cecil H. and Ida Green Professor in Techniques Biology Science.
This initially era of CRISPR-engineered PUFs supplies the signifies for researchers to validate that the cells had been created by a given firm or lab, a procedure identified as provenance attestation. With more study, the engineers intention to create a approach for monitoring the age of a precise copy of a cell line.
“Organizations establishing mobile strains are producing a massive investment decision,” Bleris claimed. “We require a way to differentiate amongst 1,000 copies of the identical solution. Even however the products are equivalent, every single of them has a special identifier, which are not able to be replicated.”
Makris mentioned that the business of producing engineered cells is so new that corporations are focused on monetizing their investments instead than on security and provenance attestation. He mentioned the semiconductor market was the similar way at very first till counterfeiting and tampering incidents highlighted the have to have for safety steps.
“We imagine that this time maybe we can be forward of the curve and have that functionality formulated by the time the sector realizes they will need it,” Makris explained. “It will be also late when they know they acquired hacked and anyone monetized their IP.”
Other authors of the research contain Dr. Yi Li, bioengineering exploration scientist Mohammad Mahdi Bidmeshki Ph.D., a former postdoctoral researcher in Makris’ lab Taek Kang, a biomedical engineering doctoral university student and Eugene McDermott Graduate Fellow and Probability M. Nowak, a bioengineering graduate scholar.
Very safe physically unclonable cryptographic primitives centered on interfacial magnetic anisotropy
Yi Li et al, Genetic actual physical unclonable functions in human cells, Science Innovations (2022). DOI: 10.1126/sciadv.abm4106
Quotation:
New technological know-how protects authenticity of engineered cell strains (2022, June 6)
retrieved 13 June 2022
from https://phys.org/news/2022-06-technology-authenticity-mobile-traces.html
This doc is issue to copyright. Aside from any truthful working for the purpose of personal study or research, no
section may perhaps be reproduced without the composed permission. The articles is offered for info needs only.