How to fix the Windows 0x0000011b network printing error


A Home windows safety update produced in January and now fully enforced this thirty day period is producing Windows people to working experience 0x0000011b faults when printing to network printers.
In January 2021, Microsoft launched a stability update to resolve a ‘Windows Print Spooler Spoofing Vulnerability’ tracked as CVE-2021-1678.
“A security bypass vulnerability exists in the way the Printer Remote Technique Get in touch with (RPC) binding handles authentication for the distant Winspool interface,” clarifies a assistance bulletin about the vulnerability.
When the security update was produced, it did not instantly safeguard products from the vulnerability. Nevertheless, it did insert a new Registry essential that admins could use to improve the RPC authentication level applied for community printing to mitigate the vulnerability.
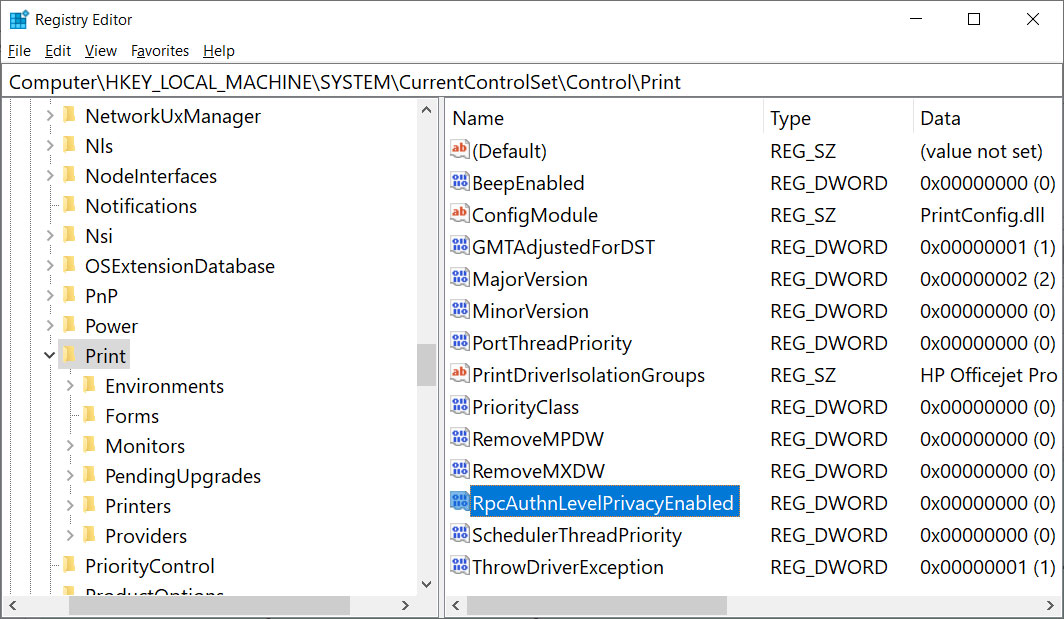
In other words and phrases, this security update did not fix any vulnerability except if a Home windows administrator established the adhering to Registry key:
[HKEY_LOCAL_MACHINESystemCurrentControlSetControlPrint]
“RpcAuthnLevelPrivacyEnabled”=dword:00000001
Nonetheless, in this month’s September 14th Patch Tuesday protection updates, Microsoft automatically enabled this placing by default for each and every Home windows system even if that Registry setting was not produced.
When this mitigation was enabled by default, Windows users started encountering 0x0000011b glitches when printing to network printers.
This printing mistake is mainly observed in smaller company and household networks that are unable to acquire benefit of a Kerberos setup on a Home windows area.
Uninstalling September’s Windows stability updates will resolve the trouble, but now the devices will be vulnerable to two vulnerabilities, PrintNightmare and MSHTML, actively exploited by threat actors.
A greater strategy is to disable the mitigation for CVE-2021-1678 until finally Microsoft comes out with new advice, as that vulnerability is not actively exploited.
How to take care of the 0x0000011b printing errors
To fix the modern 0x0000011b printing errors devoid of removing the existing Home windows Updates (KB5005565), you can as an alternative disable the CVE-2021-1678 mitigation enabled by default this thirty day period.
To do that, open up the Windows Registry Editor and navigate to the HKEY_Regional_MACHINESystemCurrentControlSetControlPrint critical, create a new DWORD-32 little bit value named RpcAuthnLevelPrivacyEnabled, and established it to , as proven in the Registry file under.
Windows Registry Editor Edition 5.00
[HKEY_LOCAL_MACHINESystemCurrentControlSetControlPrint]
“RpcAuthnLevelPrivacyEnabled”=dword:00000000
To make it less difficult to incorporate this improve, you can use the resolve-0x0000011b.reg Registry file to increase it for you.
Obtain this file on both of those your print server and your Home windows devices connecting to it, double-simply click on it, and make it possible for the data to be merged.
At the time you disable this mitigation, you will no extended be guarded from the vulnerability, but it will hopefully permit you to print once more.
If this does not address your trouble, use the help-RpcAuthnLevel.reg to go back to the Home windows defaults.